The List of Devices Which are use by Black Hat Hackers for Hacking.
As we know there are many hackers try to hack many systems but we have many questions like how to do that , how they are hack the system ,which devices use for hacking ? so for this we have some great useful devices which are use by black hat hackers for hacking.
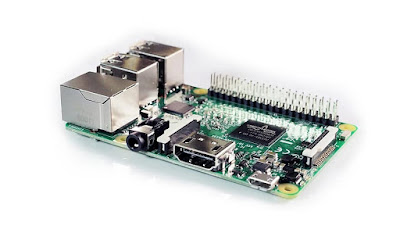
The Raspberry Pi may be a series of small single board computers developed within the uk by the Raspberry Pi foundation to market the teaching of basic computing in schools and in developing countries. the original model became much more popular than anticipated selling outside of its target marketplace for uses like robotics peripherals including keyboards mice and paces aren’t included with the Raspberry Pi. some accessories however have been included in several official and unofficial bundles. we are now on the third generation of those low budget computers which may be utilized in multiple way a classic example in security audits is to use a Raspberry Pi with it’s appropriate battery pack a distrib.
2. Wi-Fi pineapple
The Wi-Fi pineapple registered nano and tetra are the sixth generation leading platforms from hak5 thoughtfully developed for mobile and protracted deployments. they repose on over eight years of Wi-Fi penetration testing expertise at the core of the Wi-Fi pineapple is prime AP and offense suite of wireless penetration testing tools for reconnaissance man-in-the-middle tracking logging and reporting utilizing our unique hardware design PI.
Ap is that the most effective rogue access points suite available simplicity is vital to any successful audit which is why management of the Wi-Fi pineapple is conducted from an intuitive web interface built on modern standards for speed and responsiveness. the gorgeous web interface puts the penetration tester in control from any device with a stress on usability and workflow due information.This device is favorite of black hat hackers.
When the Wi-Fi landscape is available at a look advanced attacks are always clicks away with intelligent contacts to menus from clients to access points as a platform the Wi-Fi pineapple is home to numerous community developed modules which had features and extend functionality modules install food directly from the online interface and seconds developing modules is formed straightforward with an API friendly to coders at any experience level.
3. Alpha network board
A classic Wi-Fi board for injecting packets the Alpha stands out for the standard of its materials and for its use of chipsets which can be set to monitoring mode a requirement for Wireless audits.
4. Rubber ducky
The USB rubber ducky may be a keystroke injection tool disguised as a generic flash drive Computers recognize it as a daily keyboard and accept pre-programmed keystroke payloads at over 1,000 words per minute payloads are crafted employing a simple scripting language and may be wont to drop reverse shells inject binaries brute force ping codes and lots of other automated functions.
For the penetration tester and systems administrator since 2010 the USB rubber ducky has been a favourite among hackers penetration testers and IT professionals with origins because the first dinner automation had using an embedded dev board it’s since grown into a full-fledged commercial keystroke injection attack platform the USB rubber ducky captured the imagination of hackers with its simple scripting language formidable hardware and covert design.
5. LAN turtle
The LAN turtle may be a covert systems administration and penetration testing tool providing stealth remote access network intelligence gathering and man-in-the-middle monitoring capabilities housed within a generic USB Ethernet adapter case the land turtles covert appearance allows it to blend into many IT environments the land turtle is full of features for remote access man-in-the-middle and network recon everything the land turtle does may be a module and you’ll download new ones right to the device from the module marketplace keen on writing a module code one in bash Python or PHP
with a dead simple API.
6. Hack RF1
This tool installs a strong SDR software-defined radio system in other words it’s essentially a radio communication device which installs software to be utilized in place of typically installed hardware this manner. it is capable of processing all types of radio signals starting from 10 megahertz to 6 gigahertz from one peripheral which can be connected to the PC via a USB port.
The hacker phone may be a new software-defined radio that has recently been shipped bent Kickstarter funders it is a transmit and receive capable SDR with a touch ADC 10 megahertz to 6 gigahertz operating range and up to 20 megahertz of Benwood it can now be pre-ordered for 299 US dollars we just received ours from backing the Kickstarter in here’s a quick review of the product he didn’t do any quantitative testing and this is often just a first impression review thus far we’ve only tested receive on Windows SDR.
7. UBERTHOOT ONE
Uberthoot one is an open source 2.4 gigahertz wireless development platform suitable for Bluetooth experimentation supported the powerful LPC 175 X ARM Cortex in three microcontroller with full speed USB 2.0 Uberthoot one may be a good way to develop custom class one comparable Bluetooth devices. the whole board is only two and a half inches long with the USB via connector at one end and another.
RP SMA connector at the opposite one thing that sets the uber tooth aside from other Bluetooth development platforms is that it’s capable of not only sending and receiving 2.4 gigahertz signals but can also operate in monitor mode monitoring Bluetooth traffic in real time this operating mode has been
present in low-cost Wi-Fi modules for years and has found myriad uses in research development and security auditing but no such solution existed for the Bluetooth standard so far also because it is a fully open source platform software and hardware the schematics and code are readily available for all of your hacking needs.
8. Proxmark 3 kit
The proxmark is that the only SDR target NFC and therefore the frequencies that is capable of both transmitting and receiving while meeting the timing requirements of most proximity protocols the proxmark also provides full control over the radio layer additionally to software support for several higher-level protocols X l’affaire the LF antenna enables communication with tags that operate at 125 kilohertz and 134 kilohertz including hid procs to hit attack and DM 4100 the HF antenna enables communication with types operating at 1356 MHz including the fair classic ultralight and that i class.
9. Lockpicks
It’s important to remember that in some countries possession of lockpicks may be a criminal act we don’t recommend any activity that would be against the law whose verify the regulations in your country before acquiring any of those tools these tools are the most equipment utilized in lock baking in other words the art of opening a lock or a physical security device by analyzing or manipulating its components logically without the first team there are great many sizes and formats or kits which in many cases can threaten physical security.
10. Keylogger
An old classic for a login keystrokes this device are often connected via USB or PS / 2 and creates a stealthy connection between the keyboard and PC logging every keystroke in fact it tends to travel undetected by most security systems.
This are the devices which are use for hacking by black hat hackers. i hope you will get one of this devices for trials or use. all devices are easily available on online e-commerce platform.












Leave a Reply